Tactical Maritime Domain Awareness Through Edge-First Multi-Sensor Data Fusion
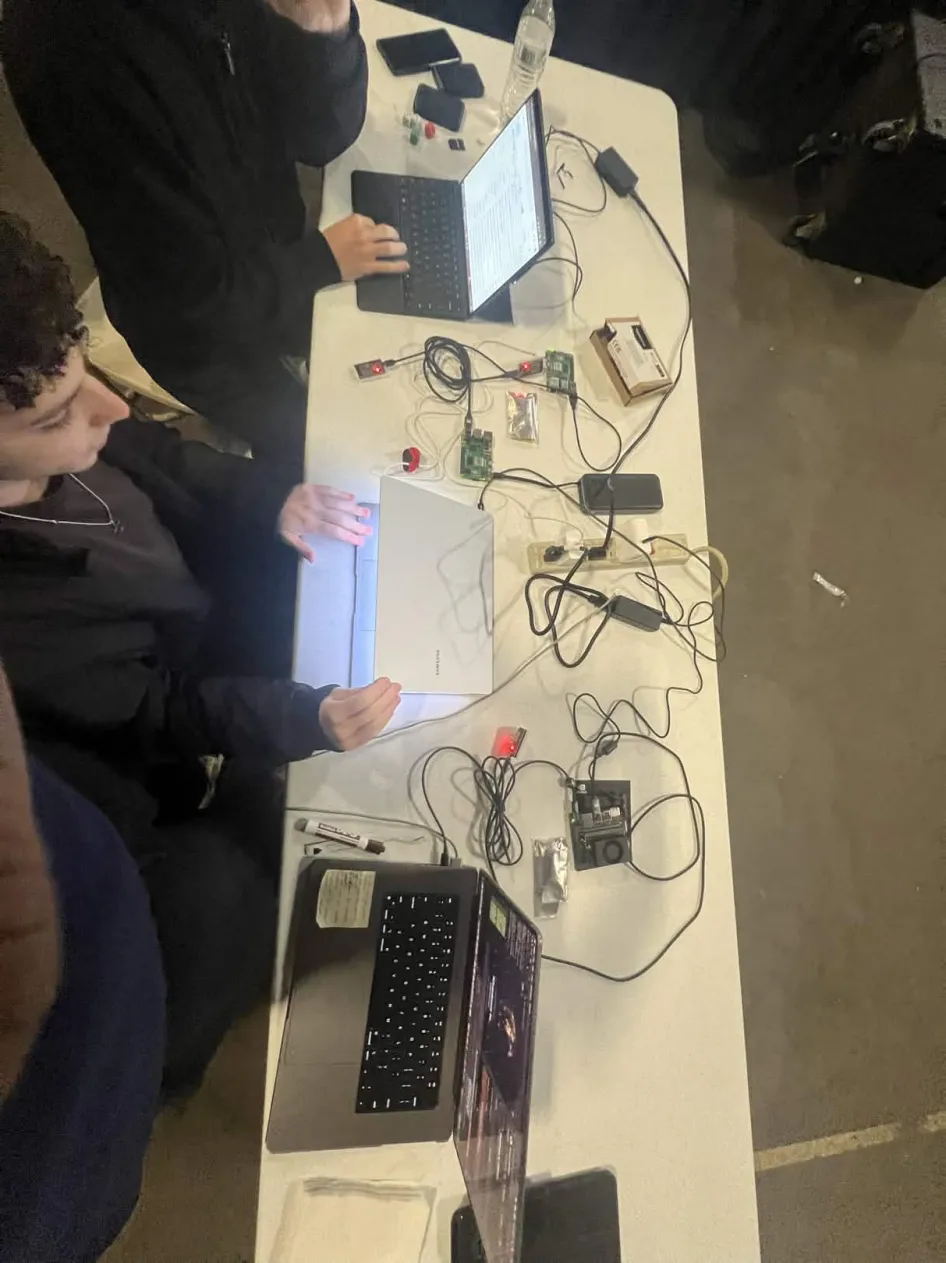
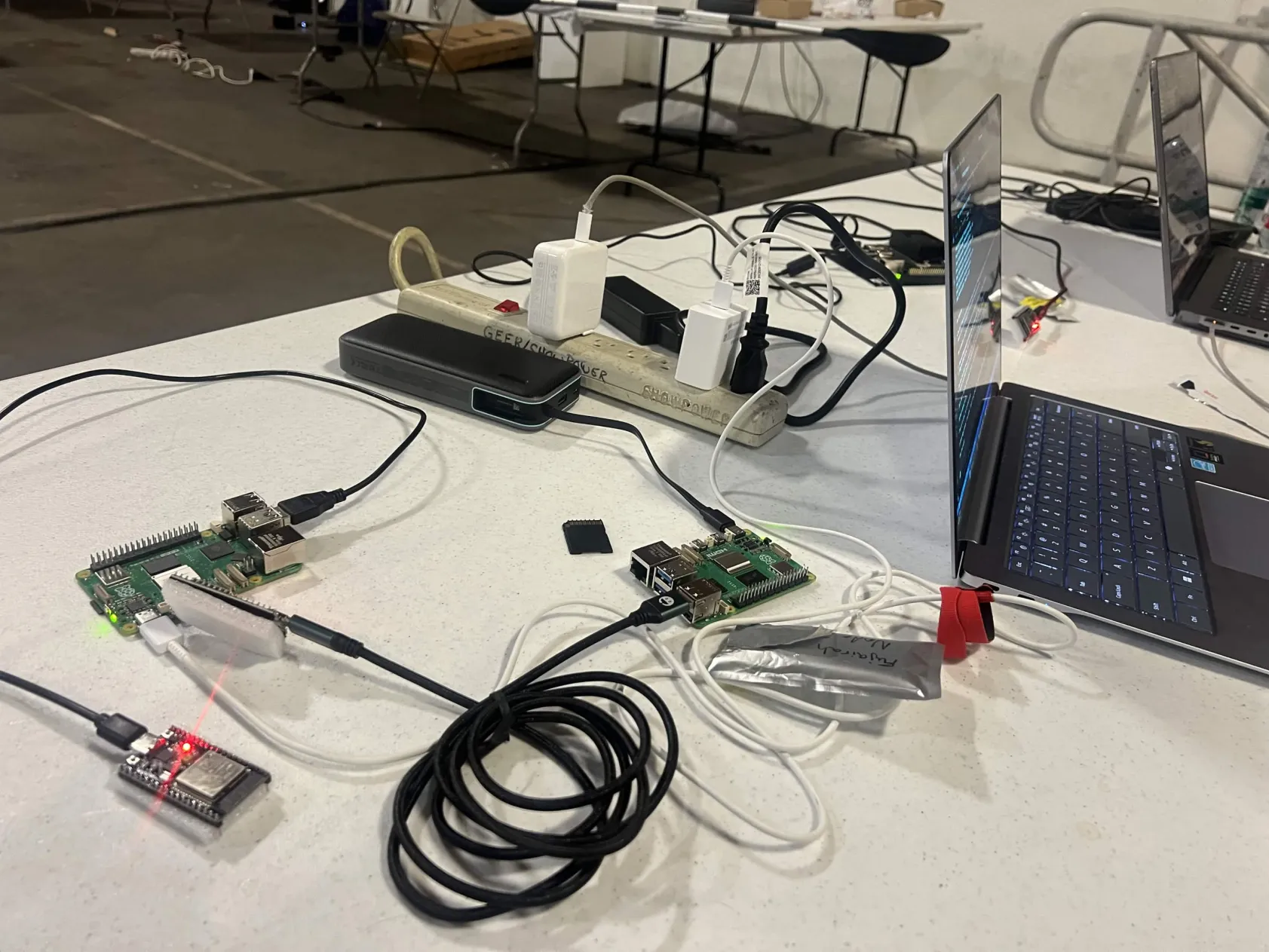
An edge-first, cloud-independent maritime threat detection system for the Strait of Hormuz. Built on a peer-to-peer encrypted mesh network using Raspberry Pi 5s, ESP32 nodes, and a Jetson Orin Nano, all for under $450.
Project Overview
The Problem
Existing maritime surveillance systems rely on cloud infrastructure, suffer 200-1000ms latency, and fail completely in denied or degraded environments. The Strait of Hormuz sees 21 million barrels of oil pass through daily, with 95% of global trade moving by sea.
Adversaries exploit these gaps through AIS spoofing, dark transits, coordinated fast-boat attacks, and mine-laying operations, all invisible to traditional cloud-dependent systems.
Our Solution
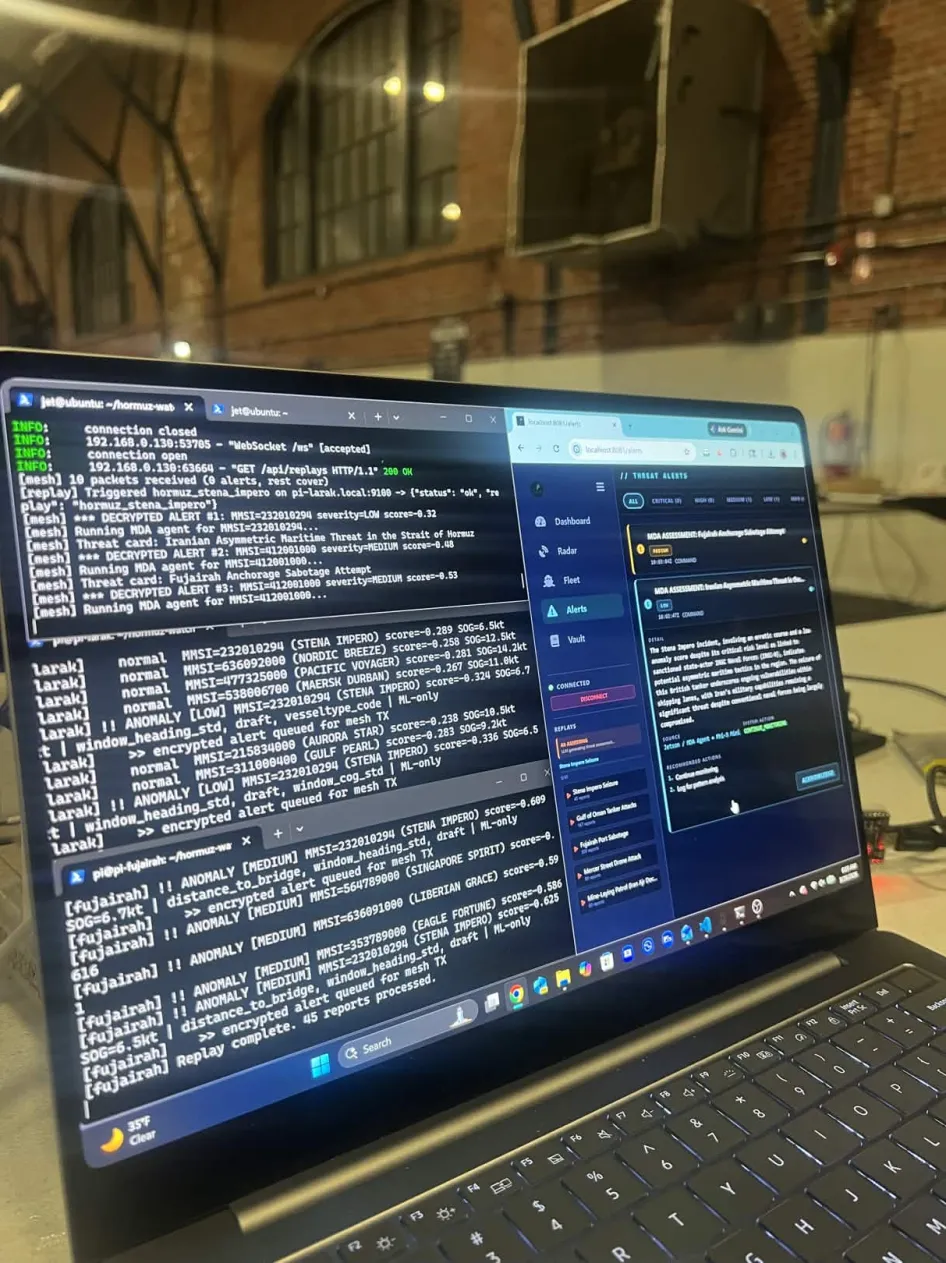
Hormuz Watch is an edge-first, fully offline maritime domain awareness system. Sensor to commander with sub-15ms latency on $450 of hardware with zero cloud dependency.
We built a peer-to-peer encrypted mesh network using Raspberry Pi 5s for edge ML detection, ESP32 nodes for encrypted relay, and a Jetson Orin Nano running a local LLM for contextual threat assessment, all communicating over AES-256-GCM encrypted channels.
System Architecture
DETECT
Edge ML anomaly scoring on Raspberry Pi 5 with Isolation Forest + Autoencoder ensemble. Processes 18 features per AIS report in under 15ms.
RELAY
AES-256-GCM encrypted ESP32 mesh network with constant-rate cover traffic. Real and dummy packets are cryptographically indistinguishable.
ANALYZE
Local LLM (Ollama + Phi-3 Mini) on Jetson Orin Nano with RAG vault of 151 intelligence documents for contextual threat assessment.
ACT
Zero-latency dashboard with Leaflet-based mapping, WebSocket broadcast, and React Native mobile app for tactical awareness.
Hardware Stack
Total deployment cost: ~$450 • Footprint: <20MB
Raspberry Pi 5 (16GB)
Edge Detection NodesRuns AIS ingestion pipeline and ML scoring engine. Two nodes deployed: Pi-Larak and Pi-Fujairah. Processes 18.8M-record trained model with USB serial interface at 115200 baud.
ESP32 Mesh Nodes
Encrypted Relay NetworkPeer-to-peer ESP-NOW 2.4GHz radio with ~150m WiFi range (2-15km with LoRa). Fixed 238-byte encrypted packet structure with constant cover traffic every 5 seconds.
Jetson Orin Nano
Command NodeJetPack 6.x environment running Ollama + Phi-3 Mini (4GB LLM), FastAPI + uvicorn backend, serial listener for mesh decryption, and WebSocket broadcast to all connected dashboards.
Machine Learning Engine
Ensemble Architecture
Trained on 18.8 million real AIS reports from NOAA MarineCadastre (USCG records, June 2024). The ensemble combines two models:
100 trees, 200K subsample, ~4.7MB, detects global anomalies in vessel behavior patterns
18→12→6→12→18 architecture, ONNX export, ~4KB, captures subtle reconstruction errors in vessel trajectories
Total model footprint: ~5MB • 82 distinct vessel-type baselines
18 Features Per AIS Report
Speed over ground, speed delta, heading change rate, course over ground, time gap
Vessel name, vessel class, dimensions, speed-to-size ratio
Distance to shipping lane, port, and geographic chokepoints
Heading std dev, speed trend, course std dev, anomaly count (rolling)
Sliding window: last 20 reports per MMSI (Maritime Mobile Service Identity)
Encrypted Mesh Network
238-Byte Packet Structure
Security & Routing
AES-256-GCM Encryption
Every packet encrypted with fixed 238-byte size. Real and dummy packets are cryptographically indistinguishable. Tamper detection via GCM authentication tag failure.
Cover Traffic
Dummy packets transmitted every 5 seconds to defeat traffic analysis attacks. An adversary monitoring the mesh cannot distinguish real alerts from noise.
Flood Relay with Deduplication
TTL=3 hop limit with FNV-1a hash deduplication using a 16-entry ring buffer per node. Prevents packet loops while ensuring delivery.
Intelligence & LLM
RAG Intelligence Vault
151 structured intelligence documents powering contextual threat assessment with 94% cross-reference rate via wiki-link methodology.
Stena Impero, Gulf of Oman, Fujairah
Known good/bad profiles, MMSI, sanctions
IRGC, IRISL, 22 shell companies
Fast-boat swarms, AIS dark transit, mines
Hormuz, Bandar Abbas, TSS lanes
Behavioral & structural anomaly indicators
OFAC advisory context, SDN mappings
Intel reports, OSINT, published analysis
Local LLM Threat Assessment
Ollama + Phi-3 Mini (4GB) running entirely on the Jetson Orin Nano, zero cloud dependency, sub-2-second response time. The LLM generates structured threat cards with contextual intelligence.
Query Workflow
ML anomaly score crosses severity threshold
Top-5 chunks retrieved by term frequency (~2,000 char context)
Zone matching, OFAC SDN list validation, multi-sensor fusion
Phi-3 Mini processes alert data + vault context via structured prompt
Title, summary, indicators, confidence score, recommended action
Fallback: rule-based threat card generation if LLM is unavailable, graceful degradation at every layer.
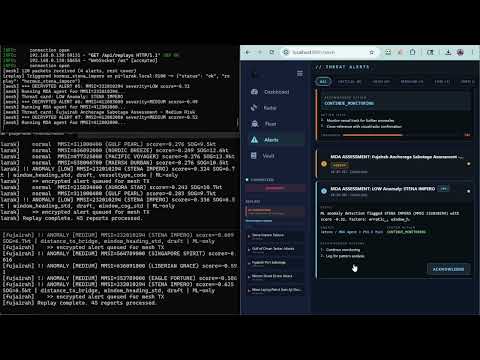
Validation Results
Incidents Detected
Recall Rate
Report Throughput
Validation Tests
5 Real Hormuz Incidents
Three fast boats at 35 knots, tanker AIS blackout, forced course reversal
Limpet mine damage, rapid deceleration signature detected
Four anchored tankers, simultaneous AIS gaps, coordinated pattern
Three drone strikes, 20-minute AIS gap, vessel slowed to 3 knots
Stop-start pattern every 500m at 3 knots in shipping lane
How We Validated
We replayed 672 real AIS reports from 5 historical Strait of Hormuz incidents through our ML pipeline. Each incident exhibited distinct anomalous signatures, fast-boat swarms, AIS blackouts, sudden deceleration, and stop-start mine-laying patterns.
The ensemble model correctly flagged all 5 incidents with appropriate severity classifications, achieving 100% recall with zero manual tuning. The system sustained 137 reports/second throughput during replay.
Real-World US Incident Validation
Project Gallery